If full correlation is in play (a leak with known passwords), then the cost doesn't make a ton of difference, because each hash can be targeted with john's --single mode or hashcat's -a 9.
And for hashes that cannot be correlated, targeting a single hash slows the attacker down only so much (because single-hash performance has to be tolerable for user experience). When the bcrypt cost gets to 12, and a million candidate passwords, that's only about 30 seconds with hashcat on 2 4090s.
And then that cost is magnified when it's a broad attack (many hashes targeted simultaneously), Even just trying the first N thousand most common passwords, attempting to crack a million bcrypt cost 12s is correspondingly harder, so there's still a "herd health" benefit to the hashes being stronger.
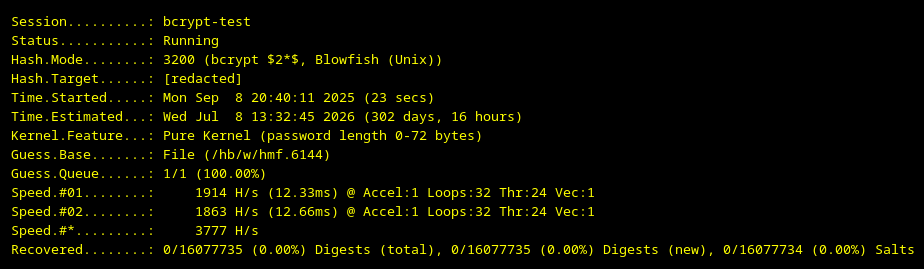
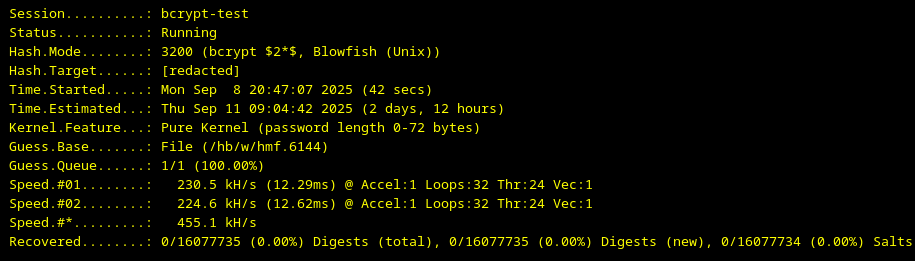
For example, with 16 million cost 12 bcrypts, and a very short list of very common passwords (6144 words, the minimum for certain hashcat efficiencies), 2x 4090s will take 300 days to fully exhaust. The equivalent attack - all other variables constant, but dropping the bcrypt cost from 12 to five -- will complete *in 2.5 days*.
And that's for a *very* short wordlist. Running through longer wordlists would be correspondingly longer.
So I think that the work factors should be tuned to protect folks who aren't reusing their own passwords across multiple accounts, but might be sharing semi-common passwords *with other users*.